Tools Used
- IDA Pro
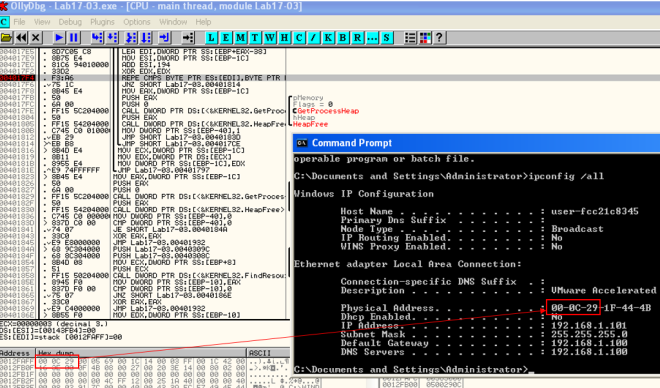
- Ollydbg
Sample:
- Lab17-03.exe SHA256: b3b4c065849c81d856558e9cf91e8cef5d481648fd8aa88cdda534ab6b75e988
VirusTotal:
- Detection Rate: 44/56
- Analyzed on 2016-03-20
-
Compilation Date: 2011-10-14 19:35:33
- View report here
Lab 17-3
Analyze the malware Lab17-03.exe inside VMware. This lab is similar to
Lab12-02.exe, with added anti-VMware techniques.
Questions
1. What happens when you run this malware in a virtual machine?
The malware terminates.
2. How could you get this malware to run and drop its keylogger?
we can patch the jump instructions at the following address
- 0x004019A1
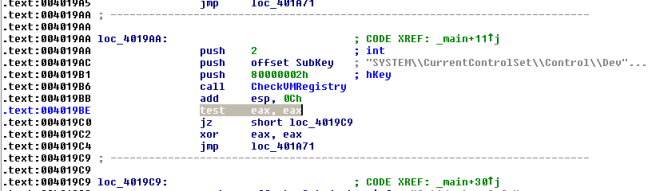
- 0x004019C0
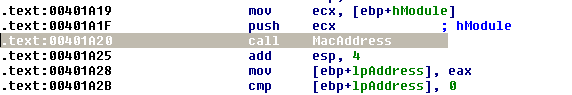
- 0x00401A2F
- 0x00401467
3. Which anti-VM techniques does this malware use?
@00401A80: I/O communication port

@004011C0: checking registry key SYSTEM\CurrentControlSet\Control\DeviceClasses\vmware

@00401670: checking mac address
@00401130: checking for vmware process name (hash of first 6 chars)

4. What system changes could you make to permanently avoid the anti-VM
techniques used by this malware?
- Patch the binaries
- Change Mac Address
- Remove VMware tools
5. How could you patch the binary in OllyDbg to force the anti-VM techniques
to permanently fail?
Change the following instruction to xor instead
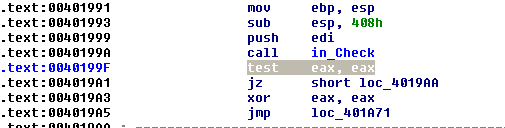
Change the following instruction to xor instead
Nop out the calling of this subroutine
Change the hash to AAAAAAAAh to invalidate the search
